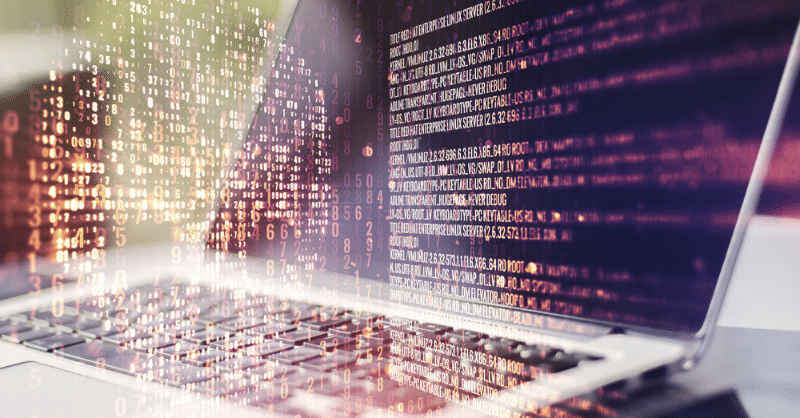
The evolution of modern technology brings lots of benefits and challenges. With the advanced opportunities that the latest software and tools present, the security issue has become prominent. With advanced technology implemented in every sphere of life, getting a fast response to cyber threats is becoming an issue. Companies must ensure the best possible cyber security when dealing with numerous cyber threats. It includes the use of ethical hacker s’ assistance.
Ethical hackers play a significant role in helping catch cybercriminals. In fact, many companies tend to employ ethical hackers to help fight against cybercriminals. Besides, hackers can help to deal with any vulnerabilities your system has. They allow checking and evaluating all the cyber security methods the company uses carefully. Further, they help deal promptly with any informational threats.
Table of Contents
Who is an Ethical Hacker?
An ethical hacker is a specialist in computer technology and programming who follows numerous ethical guidelines. Ethical hackers are often called white-hat hackers. They are a security force since they use their hacking skills to maintain the company’s proper IT infrastructure. In addition, they work to prevent cyberattacks and hacking.

The hackers also analyse, identify, and fix weaknesses of the corporation’s security system. They can hack a system to check its preparedness for possible cyber-attacks. Once the establishment employs hackers, they expect to learn the potential failure points of their system. The purpose is to prevent any criminal activity targeted at the company.
Ethical hackers can have the same skills that cybercriminals have. Still, they surely work on the right side. Lots of companies appreciate the work done by white-hat hackers. That is why their fees are quite impressive. Modern companies are ready to pay big money to protect their businesses from possible cyberattacks.
Experienced hackers always take care of the company’s and individual’s safety. Thus, once performing their tasks, they use the robust VPN. This particular security tool ensures unidentified work and brings an upgraded convenience with VPN no logs. The clever hackers use all the provided advantages of VPN to arrange smooth and safe work. It is easy to switch VPNs. Besides, VeePN ensures protected and anonymous access to any network, including the Internet.
What Do Ethical Hacker Do?
All ethical hackers work to identify the flaws of the security system and help with fixing the vulnerabilities. Hacking an analysed system is exactly what ethical hackers do. Once hacking the defined system, hackers pay attention to how easy it is to gain and maintain access, scan the system, and cover tracks. The entire hacking routine starts with gaining permission and ends with providing a report. This is a full-scale investigation aimed at checking the system’s vulnerabilities.
It is always better to find out that your system has flaws in advance. No one wants to find out about colossal security system flaws after being attacked or hacked by cybercriminals. Cybersecurity issues are essential for every company. You cannot maintain a successful business online if you are an easy target for cybercriminals. Certain standards of cyber security must be followed. This is the only way to ensure a required top level of security.
What Knowledge Do You Need to Be
an Ethical Hacker?
To become an expert ethical hacker, one must have a proper education, experience, and the right certification. The proper ethical hacking degree for ethical hackers focuses on Cybersecurity and Information Assurance. The hackers gain critical knowledge when starting Cybersecurity and Information Assurance or allied courses. Therefore, it is good if you develop your knowledge in the field with constant training and competitive practices.
Partaking in cyber defence competitions is always beneficial as well. To get one of the well-paid certified ethical hacker jobs, you must have proper ethical hacker certification. It will help secure a decent job in one of the top companies. Moreover, you can have working experience in information systems security before starting your work as an ethical hacker.
Eventually, you can gain the accreditation of a Certified Ethical Hacker (CEH). Various accreditation bodies can provide the necessary certification. You get an accreditation once passing a test. You can do it after two years of being employed in the information security (InfoSec) field or by completing special training.

Technical Skills Required from a Ethical Hacker
Ethical hackers should have proper technical skills to be on top of their game. There are many requirements for specialists to be hired by top companies. These technical skills can be gained after passing one of the information systems courses. Also, the job and constant experience in the InfoSec field can help obtain the needed proficiencies.
The key opportunities for hackers are ensured when they have enough technical abilities and experience. Therefore, it is vital to be familiar with a list of requisite programming skills. They mostly include good knowledge of HTML, JavaScript, Python, SQL, and C++. To gain a great experience once working as an ethical hacker, an understanding of Linux is obligatory.
Networking Skills
The main technical skill required from hackers is great networking expertise. Once the specialist is aware of how the computer network operates, he can easily figure out the weak links in the network easily. The computer network connects many devices and ensures numerous paths for data to be sent and received. Therefore, with complete awareness of how the network operates, it is easy to explore and define the possible threats that can cause the network’s failure.
Computer Expertise
Every hacker must be really good at the work he does. Thus, he should know his tools excellently. Computer expertise is crucial. It ensures that a specialist knows everything about computers and related modern technologies. Also, it brings the needed set of skills for proper data processing, data management, and computer files management. The experienced specialists should be well aware of how the enterprise systems work. Expert knowledge of computer systems is quite crucial in any case.
Programming Skills
This is another crucial skill for modern hackers. Mastering programming on a proper level is indispensable since it allows fast and efficient program writing. In addition, the coding language is necessary since it provides directives for a computer on how to operate. Once knowing the imperative programming languages, a specialist can provide various instructions to personal and corporate computers.
The written code is essential for operating various programs and providing directives. There are plentiful programming languages important for hackers. It includes Python, SQL, PHP, Ruby, Perl, C, C++, and Java. The more languages the specialist knows, the better he can manage the computer’s processes.
Linux Mastery
Mostly, hackers work with open-source systems like Linux. Thus, Linux mastery is obligatory for proper work with the system and various security matters. In fact, Linux is more protected than any other nowadays available operating system. Therefore, due to the lack of serious vulnerabilities, this particular system is the most preferable.
Moreover, Linux does not even need serious antivirus protection. Still, it is not a 100% safe system. It also calls for scheduled security measures to be guaranteed.
Basic Hardware Expertise
Modern hackers should have not only computer management skills, but also understand the physical parts of a modern computer. Therefore, at least basic knowledge of hardware must be guaranteed. Thus, the specialists would be able to fix any problems with data storage, processing units, or any other parts.
To be able to hack a computer, one needs to know how exactly it operates. So, one must know what parts it consists of and how they are connected.
Reverse Engineering
Reverse engineering offers lots of insight for hackers. This particular method allows recovering vital data and specifications from examining the code. The built databases allow for generating important information fast. In the cybersecurity field, reverse engineering is used to guarantee the absence of any serious security defects in the system. The understanding of reverse engineering helps to ensure a strong system protected from cybercriminals.
Database Management Skills
Efficient database management is also mandatory. It ensures the advanced protection of all the information gathered in the databases. The understanding of the most effective ways of database management allows for ensuring hack resistant software. It also allows learning how to arrange a strong and secure Database Management System.
Cryptography Skills
Cryptography skills are essential since they help specialists keep vital information and data from third parties. These skills allow hackers to use the latest protocols to prevent third parties from retrieving and sharing sensitive information.
Cryptography ensures the safe and secure transfer of files between two parties. It allows converting information into encrypted files to be transferred safely. In addition, up-to-date hackers use cryptography skills to prevent any possible data leakage.
Problem-Solving Skills
Every modern hacker must be aware of the top efficient and fast ways of guaranteeing an advanced company’s cybersecurity. It brings a strong need for decent problem-solving skills. Moreover, every hacker must be a clever person with the ability to think critically. To arrange a hacker-resistant system, lots of testing must be conducted. It calls for a profound knowledge of the best ways to implement the top working solutions timely.
Consequences on Ethical Hacker
To start and develop a great ethical hacker career, one must have a proper education, experience, and verified certification. It is important to have all the required technical skills and capabilities. What is more, every hacker must be a clever person with a great ability to think critically. He should keep studying and improving his skills constantly to ensure a hack-proof system for the company that hires him.


5 Reasons Why You Should Pursue a Cybersecurity Career

Differentiating Web Design and Web Development

Top 10 Social Media Management Tools for Businesses in 2024

Why is Child Development so Important in Early Years




 November 08, 2023
November 08, 2023